Meta’s Argument on Fair Use and Pirated Books
In a controversial legal battle, Meta has taken a bold stance regarding the uploading of pirated books via BitTorrent, asserting that such actions qualify as fair use. This claim arises in the context of the company’s efforts to gather data for train…

Meta’s Argument on Fair Use and Pirated Books
In a controversial legal battle, Meta has taken a bold stance regarding the uploading of pirated books via BitTorrent, asserting that such actions qualify as fair use. This claim arises in the context of the company’s efforts to gather data for training artificial intelligence models. Meta, alongside other tech firms, has reportedly downloaded and shared pirated books from sources like Anna’s Archive and other shadow libraries. The ongoing lawsuit has placed the issue of copyright infringement and fair use at the forefront of discussions in the technology and legal communities.
Meta’s argument hinges on the assertion that the data obtained from these pirated books plays a critical role in establishing U.S. leadership in the global AI landscape. By leveraging this data, Meta believes it can enhance its AI capabilities, which in turn could benefit various sectors, including cybersecurity and data protection. The implications of this argument extend beyond the immediate legal context, potentially influencing how copyright laws are interpreted in the digital age.
Implications for Cybersecurity and Network Security
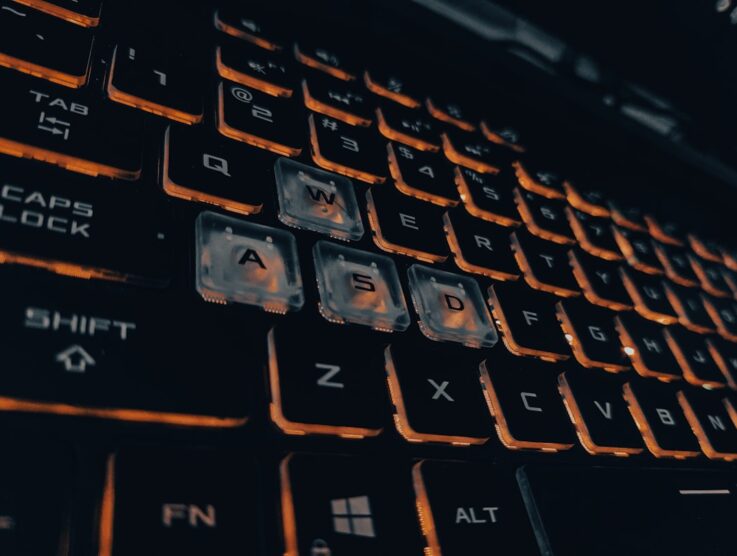
The debate surrounding the uploading of pirated books via BitTorrent raises significant concerns regarding cybersecurity and network security. While Meta argues for fair use, the act of sharing pirated content can expose users to various risks, including malware and data breaches. Engaging with pirated materials often involves navigating unsecured networks, which can compromise personal information and lead to unauthorized access to sensitive data.
Moreover, the legal ramifications of this case could set a precedent that impacts how organizations approach data protection and threat intelligence. If the court sides with Meta, it may embolden other companies to engage in similar practices under the guise of fair use, potentially leading to increased instances of copyright infringement and associated cybersecurity vulnerabilities. Users who participate in these activities may inadvertently expose themselves to legal action and security threats, underscoring the need for heightened awareness and protective measures.
Context
The intersection of copyright law and digital technology has become increasingly complex as the internet continues to evolve. The rise of platforms that facilitate the sharing of pirated content, such as BitTorrent, has prompted ongoing discussions about intellectual property rights and fair use. As tech companies seek to harness vast amounts of data for AI development, the boundaries of what constitutes fair use are being tested.
This case exemplifies the broader challenges that arise when balancing innovation with the protection of intellectual property. The outcome may influence future legislation and policy-making in the realm of copyright, particularly as it pertains to emerging technologies like artificial intelligence and machine learning.
What to do
To protect yourself in the face of these evolving cybersecurity threats, consider the following steps:
1. Update all affected software to the latest versions immediately to patch any vulnerabilities.
2. Enable automatic updates where possible to ensure you receive the latest security enhancements.
3. Monitor security advisories from affected vendors to stay informed about potential risks.
4. Use a VPN service to protect your internet traffic and maintain your privacy. Use a reliable VPN like Surfshark or ProtonVPN to safeguard your online activities.
5. Consider additional security measures like multi-factor authentication to enhance your data protection.
By taking these proactive steps, you can better safeguard your personal information and navigate the complexities of digital copyright and cybersecurity.
Source
For more cybersecurity news, reviews, and tips, visit QuickVPNs.